When establishing your home network, it's essential to focus on the security of SSH access. This includes utilizing robust measures through your router to defend your devices and data from potential threats. A secure SSH connection ensures encrypted communication between your devices and the remote server, preventing unauthorized access ssh remote access behind router and data exposures.
- Begin by selecting a strong password for your router's admin interface. Avoid basic passwords and think about a combination of upper and lowercase letters, numbers, and symbols.
- Turn on SSH access on your router and adjust it to use strong encryption protocols like SSHv2.
- Control access to SSH by configuring a whitelist of allowed IP addresses. This hinders unauthorized users from connecting to your router.
Continuously update the firmware on your router to patch any security vulnerabilities. Be aware of the latest security threats and best practices for protecting your network.
Connecting to Servers Behind a Firewall Using SSH

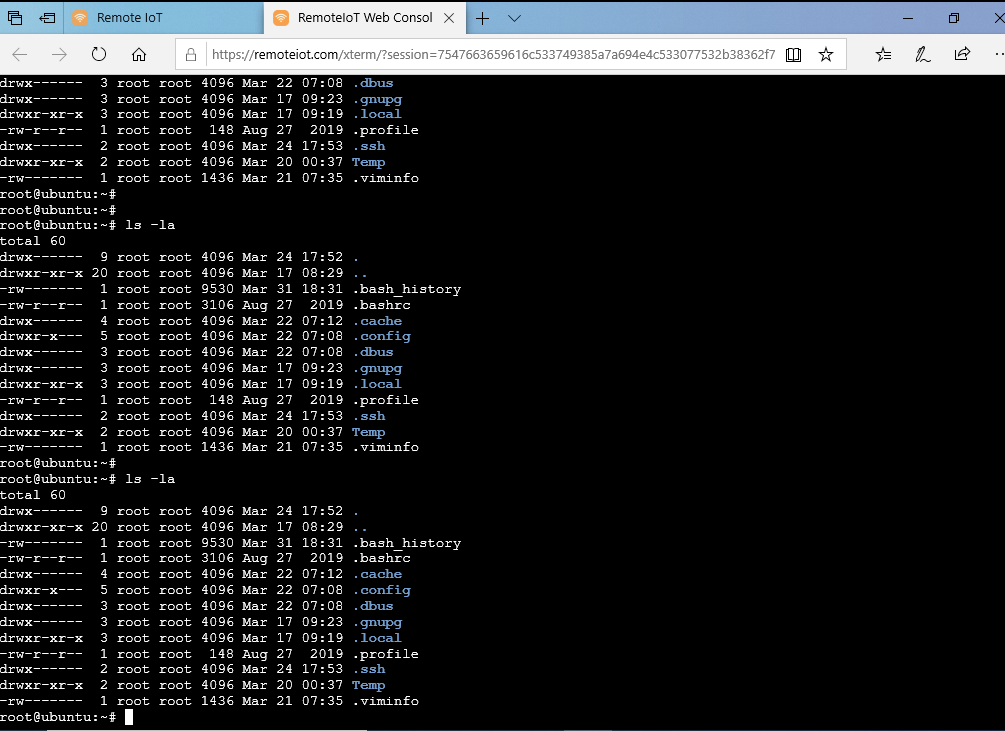
Securing your network with a firewall is crucial for protecting sensitive data and resources. However, this security measure can sometimes pose a challenge when you need to access servers located behind the firewall. Thankfully, SSH (Secure Shell) provides a robust and secure solution for connecting with these remote servers. By establishing an encrypted connection, SSH allows administrators to execute various tasks such as file transfers, software installations, and system monitoring, all while maintaining a high level of security.
To successfully reach servers behind a firewall using SSH, you'll need to configure your firewall rules to allow incoming SSH connections on the designated port, typically port 22. Once this is completed, you can use an SSH client on your local machine to build a secure connection to the target server.
Remember to always authenticate yourself using strong passwords or SSH keys for enhanced security.
SSH Tunneling: Bypassing Network Restrictions overcoming
SSH tunneling offers a robust method for reaching resources whose may be limited by network security measures. By establishing an encrypted channel between your computer and a remote server, SSH tunneling permits you to redirect traffic through this secure tunnel. This effectively obscures your actual IP address and location from the internet, enabling you to circumvent restrictions.
- Moreover, SSH tunneling can be used for enhancing security by encrypting sensitive data during transmission. Consequently, it is a essential tool for system administrators who need to remotely manage servers and software.
Establishing Remote SSH Access with Port Forwarding
Gaining remote access to your server is crucial for maintenance. SSH provides a secure protocol for this purpose. However, you often need to route traffic through a different channel to access specific services on your destination server.
This article will guide you through the process of establishing remote SSH access with port forwarding.
First, you'll need to confirm that SSH is enabled on your machine. You can typically do this by checking the firewall configuration and making sure that SSH traffic is allowed. Next, you'll need to set up port forwarding within your SSH client. This involves specifying the source port that will be used to connect to the remote server and the remote port where the service you want to access is running.
For example, if you want to access a web server on port 8080 on your remote server, you could configure port forwarding in your SSH client to use port 8081 on your local machine. When you connect to the remote server via SSH, all traffic sent to port 8081 on your local machine will be routed to port 8080 on the remote server.
Once you've configured port forwarding, you can connect to the remote server using your SSH client. After connecting, you should be able to access the service on the specified target port. Remember that the local port used for forwarding should remain available and not be in use by other applications.
Navigating SSH on NAT
Connecting securely via SSH through a Network Address Translation (NAT) firewall can sometimes present unique challenges. This guide provides a comprehensive overview of the concept, exploring common issues and presenting effective solutions. We'll delve into configuring ports, hostnames, and other techniques to ensure your SSH connections remain secure and reliable even when behind a NAT.
- Understanding the NAT Environment
- SSH Port Forwarding Strategies
- DDNS Solutions
- Troubleshooting Common Issues
- Best Practices and Security Tips
Reaching Remote Hosts via SSH and Firewalls
Establishing a secure connection to remote hosts is paramount in today's digital landscape. Secure Shell (SSH) provides a robust mechanism for verifying users and encrypting data transmission, mitigating the risks associated with transmitting sensitive information over networks. However, firewalls often serve as a crucial layer of defense, requiring careful configuration to allow SSH connections while maintaining a secure perimeter.
When configuring firewalls for SSH access, it's essential to define a clear set of rules that govern incoming and outgoing traffic. This involves determining the specific ports used by SSH (typically port 22) and granting connections only from authorized sources. Implementing strong authentication measures, such as multi-factor authorization, further enhances security.
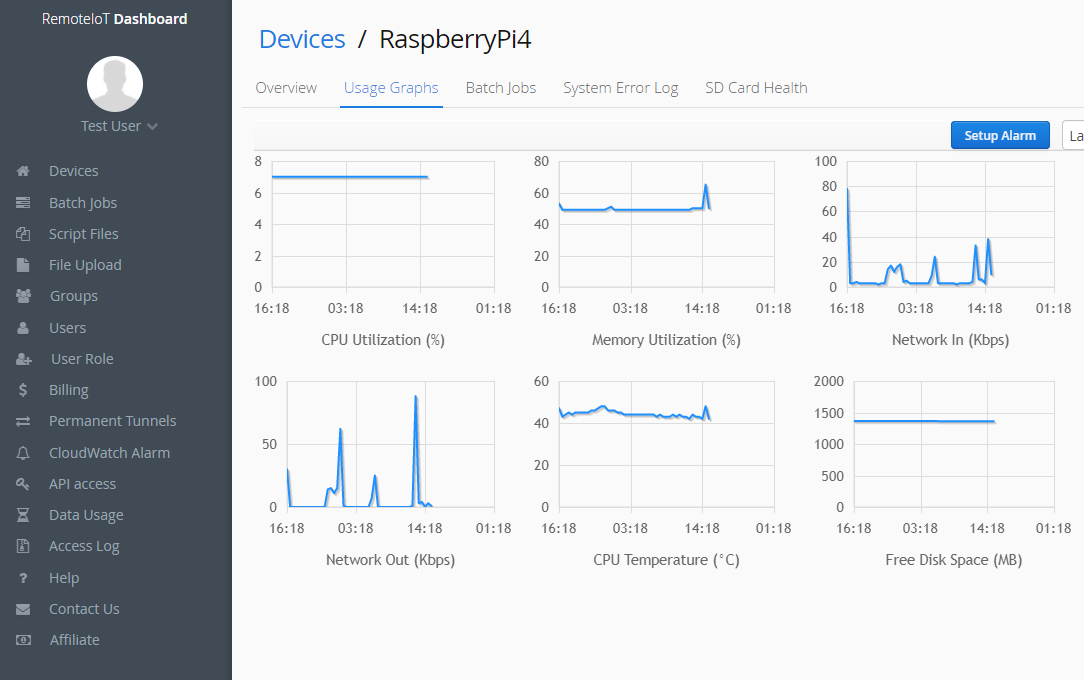
Additionally, it's crucial to keep SSH software up to date to patch known vulnerabilities. Regularly reviewing firewall logs and monitoring network activity can help discover suspicious attempts to access remote hosts, enabling timely remediation efforts.
Setting Up Router for Secure SSH Access
To ensure safe remote administration of your router, configuring secure SSH access is paramount. Begin by activating SSH on your router's interface. Next, choose a robust SSH protocol, such as SHA-256. It's crucial to generate a strong, unique password for the SSH account and avoid using default credentials. Furthermore, consider activating two-factor authentication (copyright) for an additional layer of security. Regularly upgrade your router's firmware to address potential vulnerabilities. By following these steps, you can effectively strengthen your router's SSH access and protect against unauthorized access attempts.
Remote Administration over SSH: Firewall Considerations
Securely enabling remote administration over SSH involves careful consideration of firewall settings. These primary objective is to permit incoming connections on the designated SSH port and also effectively preventing unauthorized access. A robust firewall configuration should establish a strict set of rules that explicitly define allowed IP addresses or ranges, utilizing whitelisting practices whenever practical.
It's crucial to steer clear of opening SSH access to the entire public internet. Instead, narrow down access to trusted networks or individual IP addresses, using measures like VPNs for enhanced security. Furthermore, consider implementing a firewall rule that permits only known good user accounts to initiate SSH connections. This helps mitigate the risk of compromised credentials being exploited.
Remember to regularly review and update your firewall configuration as your network environment evolves. Stay informed about potential vulnerabilities and implement necessary patches or security enhancements to ensure a secure remote administration setup.
Establish an SSH Tunnel for Remote Access
Establishing an SSH tunnel provides a secure method for off-site accessing resources on a server. By setting an encrypted connection between your local machine and the server, you can work around firewalls and access applications or data that might otherwise be unavailable. This process involves employing SSH software on both your local system and the remote server to establish a secure tunnel. The configuration process varies depending on your operating system and specific needs, but generally involves specifying the remote server's address, username, and port number.
There are several varieties of SSH tunnels, each with its own purpose and configuration. A channeling tunnel can be used to route traffic from a local port to a remote port, while a dynamic tunnel establishes a connection between your machine and a specific application on the server.
- Grasping the different types of tunnels is essential for choosing the right configuration for your needs.
- Numerous online resources and tutorials are available to guide you through the process of establishing an SSH tunnel.
Troubleshooting SSH Connections Behind a Router
When establishing Secure Shell (SSH) connections to devices behind a router, several common issues can arise.
First, ensure that your router's firewall isn't filtering incoming SSH traffic on port 22. You may need to create an exception or rule within the router's settings to permit connections on this port.
Secondly verify the IP address of the device you're attempting to connect to. Use a command like "ping" or "traceroute" from your local machine to confirm the correct IP address.
Finally, double-check your SSH connection details, including the hostname or IP address, username, and password. A simple typo can often lead to a failed connection attempt.
If you've taken care of these basic troubleshooting steps and still face connectivity issues, consider consulting the documentation for both your router and the device you're trying to connect to.
Strengthen Your SSH Access: Firewall Rules Best Practices
Securing your SSH access is paramount to maintaining a robust and safeguarded network. Implementing strict firewall rules can act as an essential barrier against unauthorized attempts to breach your systems. A well-configured firewall should permit only necessary incoming connections on the SSH port (typically 8080). Restrict access from unknown or untrusted IP addresses, and implement multi-factor authentication for an added layer of security.
- Leverage a strong firewall solution with granular control over incoming traffic.
- Establish strict access policies based on trusted users and their roles.
- Log all SSH activity for auditing purposes and to identify any suspicious behavior.
Consistently review and update your firewall rules to mitigate evolving threats.